KEEPING your phone away from snoopers isn’t just smart – it’s vital if you want to protect yourself from stalkers, fraudsters and other criminals.
But the warning signs can be easy to miss. From sudden battery drain to strange background noises and mystery apps, here’s what to look out for and the simple steps to kick them out before it’s too late. There is also an ‘Emergency’ button you need to know about too.
 Look out for this orange dot to tell if your microphone is in useCredit: Apple
Look out for this orange dot to tell if your microphone is in useCredit: Apple
Microphone
Your phone is a deeply personal gadget and you trust it with everything.
So the idea your microphone could be spying on you is unsettling. The good news? It’s easy to check if it’s being misused.
Cases are rare – but when it does happen, it’s usually down to a dodgy app secretly installed on your device.
That could be by someone you know with access to your phone or after you’ve been tricked into downloading it without realising.
There are a few ways to know if your microphone is being used.
First off, you at the top of the status bar on your .
That signals that your iPhone microphone is actively being used. You can tap it to find out how.
The next step is to see which have access to your microphone.
You can go into Settings > Privacy & Security and then look at your microphone permission.
There you’ll be able to see all of the apps that are allowed to access your phone’s mic.
If you see anything suspicious – like a calculator app that’s using your microphone – then you can revoke the permission.
Alternatively, if it’s an app that you really distrust, consider just deleting it entirely.
 You can find your app permissions in the Privacy & Security settings on your iPhoneCredit: Sean Keach / The Sun
You can find your app permissions in the Privacy & Security settings on your iPhoneCredit: Sean Keach / The Sun
The third step that you’ll want to take is switching on the .
You can find this in Settings > Privacy & Security > App Privacy Report.
This keeps tabs on all of the data and sensors on your phone, and logs when they’re requested by apps.
So if an app is tapping into your microphone, it’ll be recorded in the App Privacy Report.
You can check on the report at any time to see where your info or sensors are being used.
But just note that it only starts logging from the moment you turn the report on.
So it won’t show you anything from before you activated the setting.
And if you switch the App Privacy Report off, the next time you turn it on, it’ll be starting from scratch again.
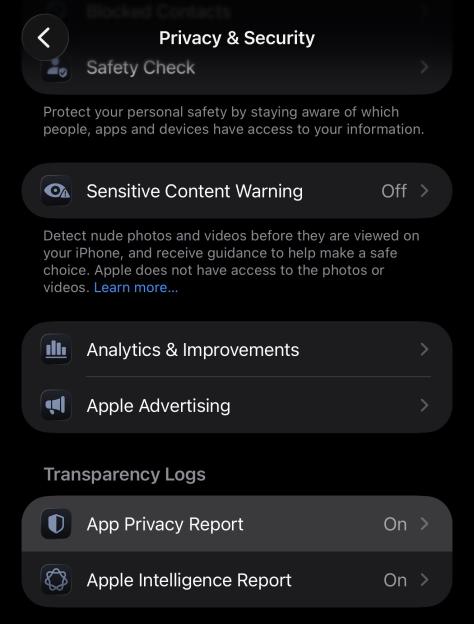 Turn on the App Privacy Report to log when your data or sensors are being accessedCredit: Sean Keach / The Sun
Turn on the App Privacy Report to log when your data or sensors are being accessedCredit: Sean Keach / The Sun
Camera
And it’s not just your microphone – your camera could be watching you as well.
Thankfully it’s just as simple to see when your iPhone camera is in use, or has been in use.
For active use, you’ll want to on the status bar – similar to the orange light used for the microphone.
And just like the microphone, your camera permissions can be found in your phone’s Privacy & Security settings.
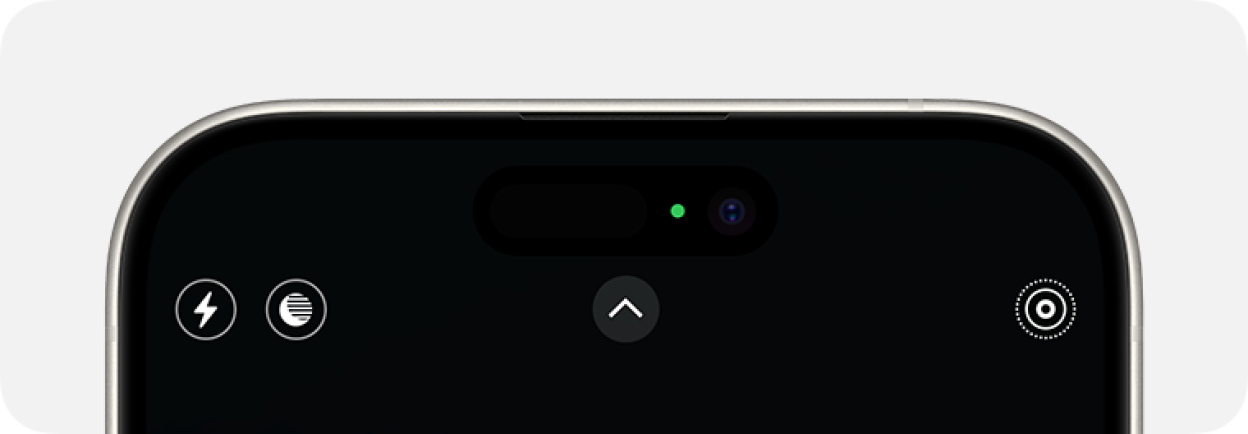 A green dot signifies that your camera is being actively usedCredit: Apple
A green dot signifies that your camera is being actively usedCredit: Apple
That way, you can see exactly which apps have permission to tap into your camera – and block them if you see fit.
As well as that, the App Privacy Report also monitors camera usage.
So if an app is repeatedly using your camera, you’ll be able to see it clearly logged in the report.
Location
There are a few ways that someone might be checking up on your location.
APPLE'S APP PRIVACY REPORT EXPLAINED
This is a seriously handy iPhone feature...
If your iPhone is running iOS 15.2 or later (it probably is but go to Settings > General > Software Update to check) then you can access the App Privacy Report.
Go into Settings > Privacy & Security > App Privacy Report and turn it on.
Once it’s on, it’ll begin logging how often apps access your data.
That includes your camera, but also your microphone, location, health data, and more.
You can see all the apps accessing this data, as well as exact timestamps for when they did it.
So you can very easily check on an app to see if it’s behaving oddly.
Uber needs your location and Instagram will likely use your camera – but does that random calculator app need access to your microphone? And why is it activating 50 times a day?
If you’re worried about an app, you can then go into Settings > Privacy & Security and shut off sensor or data access.
Or consider deleting the suspicious app entirely.
But a word of warning: the App Privacy Report only logs behaviour after it’s been switched on. So you won’t see any info from before you activated the feature.
And if you turn it off and then switch it on again, you’ll be starting from fresh.
Picture Credit: Apple / The Sun
One method is through the Find My app, which is where you keep track of your own devices.
Find My also lets you check up on the locations of willing family members.
So you might have Find My set up with your partner so you can see each other’s location.
However, you might have set this up with an ex and forgotten to remove it.
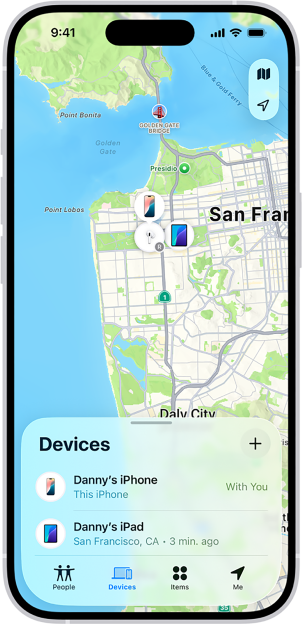 You can track devices using Apple’s Find My appCredit: Apple
You can track devices using Apple’s Find My appCredit: Apple
Or someone might have physically accessed your phone in person, added themselves to your Find My, and then gained .
Either way, it’s easily stopped.
Just go into the Find My app and check to see if your location is being shared with anyone else.
If it is, you can simply terminate the sharing arrangement right there.
Another method that someone might be using is a dodgy app that they’ve installed on your device.
This could be something that was installed by someone close to you with access to your phone.
Or it might have been installed by you unwittingly, without you realising your were downloading a dangerous app.
Thankfully it’s very easy to find the list of apps that your device is sharing your location with.
 Find My also lets you view the movements of people who have shared their location with youCredit: Apple
Find My also lets you view the movements of people who have shared their location with youCredit: Apple
And if you notice an unfamiliar app that has access to your location, you can revoke the permission.
It might also be worth deleting the app if it’s unfamiliar anyway.
Just go into Settings > Privacy & Security, look for the Location section, and then review the list of apps with the permission.
Remember: sinister apps can be disguised as something harmless like a calculator or PDF scanner. Ask yourself: why would this app need my location?
Apple Account
If someone wanted to read your text messages they would probably use your Apple account to do it.
Breaking into your Apple account would be one of the most powerful mechanisms for spying on what you’re up to.
Not only would it let someone check up on your location and look through the photos in your iCloud back-up, they’d also be able to see your iMessage texts.
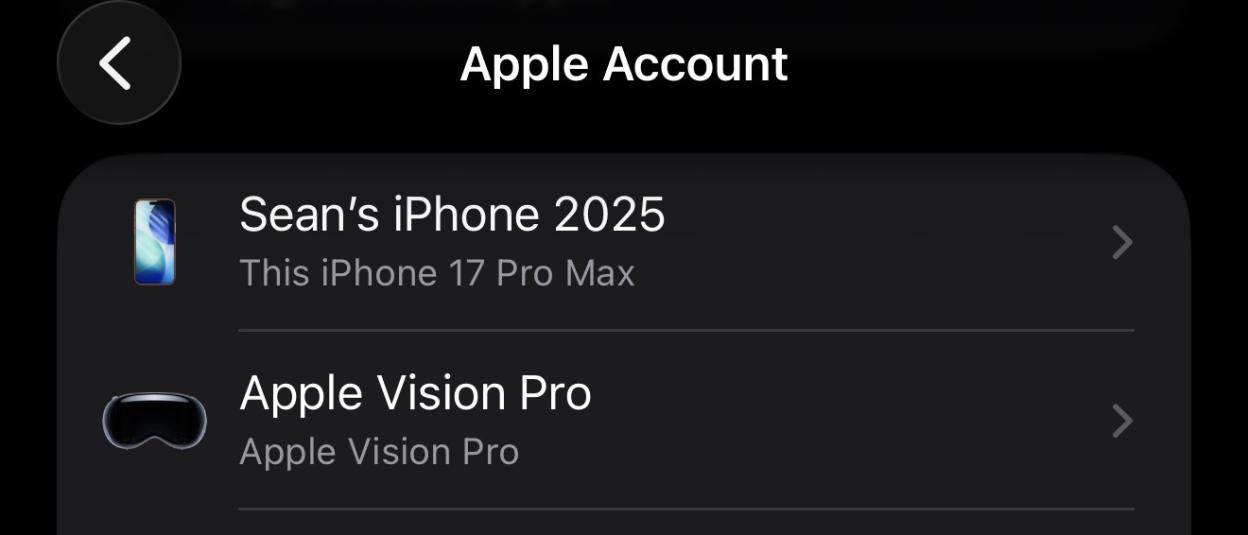 You can see the devices that are signed in with your Apple Account in your iPhone SettingsCredit: Sean Keach / The Sun
You can see the devices that are signed in with your Apple Account in your iPhone SettingsCredit: Sean Keach / The Sun
That’s obviously an enormous breach of privacy.
Thankfully, it’s very easy to see if someone else is logged into your Apple account.
Your first port of call should be going into Settings and then tapping on your name at the top.
Then when you scroll down, you’ll be able to see all of the devices that are registered to your Apple account.
It’s worth doing a regular audit of this list to make sure that there aren’t any unfamiliar devices on the list.
This is especially important if you’ve resold an old iPhone and forgot to remove it from your Apple account.
It’s worth noting that someone might be directly logging in to your account via the iCloud website.
This is harder to monitor, but you can protect against it by making sure that you use multi-factor authentication (where you need a code to log in), and a strong password that you don’t use anywhere else.
If you’re worried, it may be worth updating your password to be sure.
Sign up for The Sun Tech newsletter for gadgets, games & more
Hello! I'm Sean Keach, The Sun's Head of Technology and Science
I’ve been writing about gadgets, games and the future of technology for more than a decade.
During that time I’ve penned thousands of articles, filmed hundreds of videos, talked tech on TV and radio, and travelled around the world to bring you the latest on Apple, Meta, Google, Amazon, Netflix and more.
And I’ve got a weekly newsletter called The Sun Tech that you can read for free every Thursday.
I bring you the latest from the world of tech, including behind-the-scenes action, exclusive content, expert analysis, and plenty of help advice – so please follow along!
Screen Time
Of course, someone could be physically checking your iPhone, snooping through it in person.
This would typically only be possible by someone close to you – maybe a nosy partner, friend, family member or colleague.
Often a phone snooper would strike when you’re not looking at your phone. This could be while you’re asleep or in the shower.
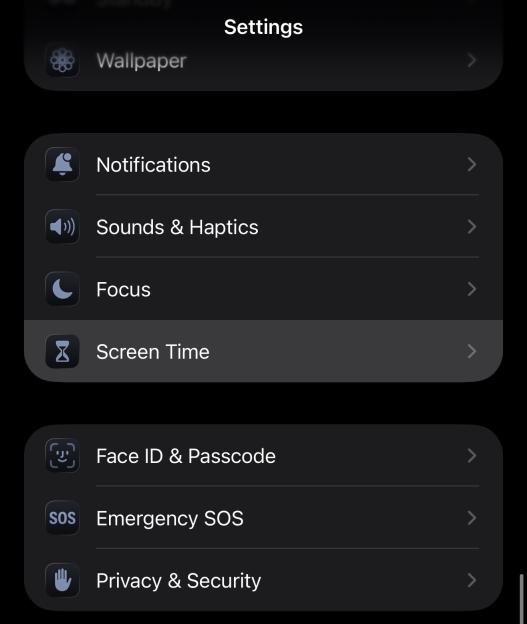 Turn on Screen Time in Settings to log phone usageCredit: Sean Keach / The Sun
Turn on Screen Time in Settings to log phone usageCredit: Sean Keach / The Sun
The good news is that it’s very easy to see when you were unawares.
You can do this using your iPhone’s Screen Time report in the Settings app.
This is meant to be a sort of digital wellbeing service that lets you monitor (and regulate) how much time you’re using your mobile.
But you can also use it to see if your iPhone was being used during the night.
You’ll need to turn on Screen Time first, so that your iPhone activity is logged.
Then go into Screen Time and tap on See All App & Website Activity.
Choose the Day tab and you’ll be able to see the exact hour slots that your phone was being used.
If you see that your phone was in use at 3am while you were tucked up in bed asleep, you’ll know that something is amiss.
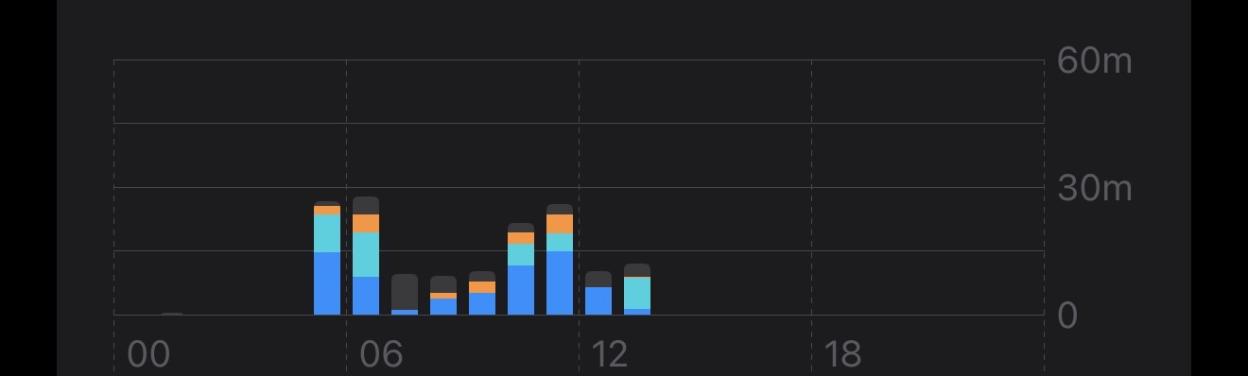 You can easily see the hours during which your phone was activeCredit: Sean Keach / The Sun
You can easily see the hours during which your phone was activeCredit: Sean Keach / The Sun
And you can also scroll down, tap on a specific app, and see the hour slots for those too.
You can’t see what the person was doing in the app, but it’s a good sign that something is going on.
Full check
If you want a catch-all way to terminate all sharing agreements, there’s a simple trick to do just that.
It’s called , and it’s a default part of – the software that your iPhone runs on.
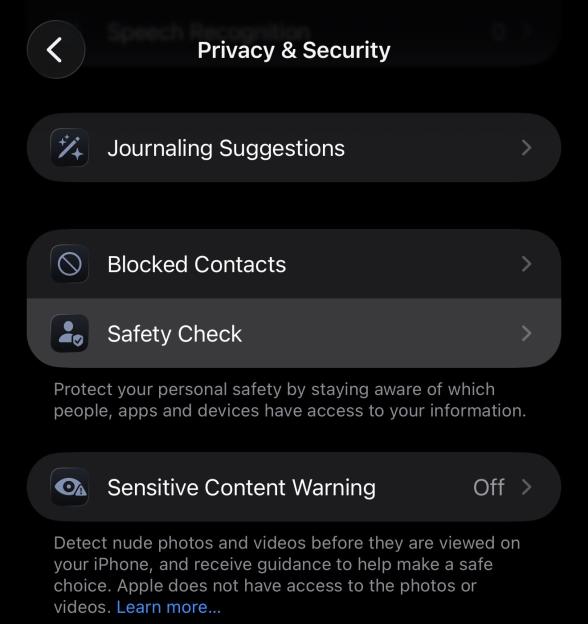 Safety Check is a quick solution for reviewing your sharing permissionsCredit: Sean Keach / The Sun
Safety Check is a quick solution for reviewing your sharing permissionsCredit: Sean Keach / The Sun
Safety Check basically lets you review all of your sharing agreements, and terminate them all in one fell swoop if you prefer.
You can find it in Settings > Privacy & Security > Safety Check.
Then you can follow the instructions to review your settings.
Or you can hit to fully cancel all permissions across your device.
WHAT SAFETY CHECK CAN'T CHANGE
Here's Apple's official list of shared info that Safety Check can't review or change...
- Non-Apple accounts and passwords.
- Social media sharing.
- Devices you’re signed into with a different iCloud account.
- An iPad or Mac with information sharing settings turned on for other apps.
Picture Credit: Apple
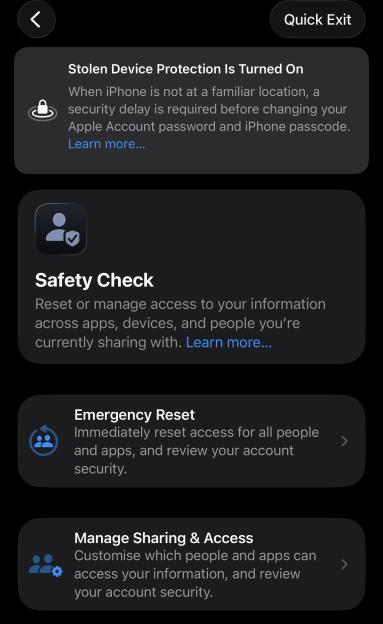 You can do an Emergency Reset to cut off all privacy permissions instantlyCredit: Sean Keach / The Sun
You can do an Emergency Reset to cut off all privacy permissions instantlyCredit: Sean Keach / The Sun
There’s also an option in the corner called Quick Exit.
This will save your changes so far, and then completely quits the app.
It’s worth regularly reviewing your Safety Check to make sure that nothing has changed.
Sharing inside apps
The other thing to watch out for is sharing agreements that you have inside apps.
WHAT CAN SAFETY CHECK LIMIT?
You can switch off access to the following...
- Bluetooth
- Calendars
- Camera
- Contacts
- Files and Folders
- Health
- Local Network
- Location Services
- Media and Apple Music
- Microphone
- Motion & Fitness
- Photos
- Reminders
- Research
- Speech Recognition
Picture Credit: Apple / The Sun
The Apple-wide system wouldn’t necessarily pick these up.
For instance, if you have a Ring doorbell, you can view the footage in your Ring app.
And it’s possible to add other people – like a family member – to that doorbell so that they can see footage and control it too.
This is a Ring setting, so Apple doesn’t have any control over that.
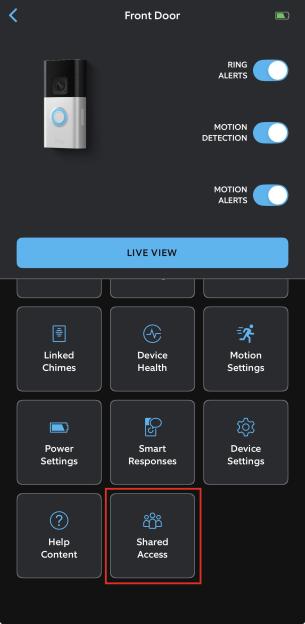 Check your smart gadget apps to see who you’re sharing your info withCredit: Sean Keach / The Sun
Check your smart gadget apps to see who you’re sharing your info withCredit: Sean Keach / The Sun
That means you’ll need to go into your Ring account to make sure that you don’t still have an ex tacked on to your doorbell, and that there aren’t any strange accounts piggybacking on your device.
Have a think about the other smart devices you have at home, and make sure that you’re not sharing them with anyone that shouldn’t be included on your account.
If you see anything suspicious, revoke the access immediately. It’s better to be safe than sorry.